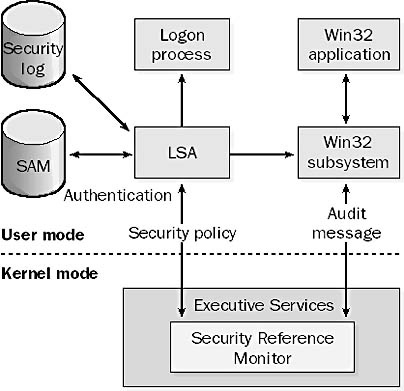
Security Architecture | CISSP Exam Cram: Security Architecture and Models | Pearson IT Certification

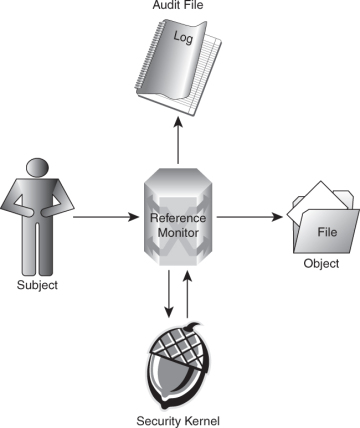
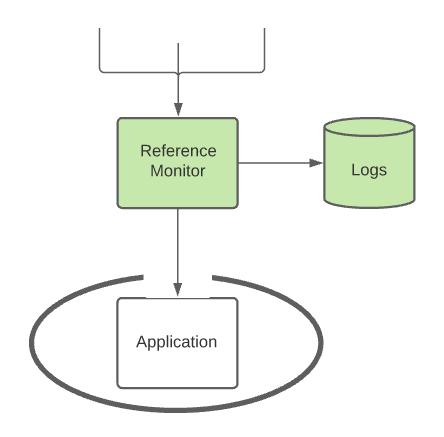
A system's security architecture. The reference monitor intercepts each... | Download Scientific Diagram
GitHub - garagakteja/Reference-Monitor-Security-Build: Restricted Python (Repy) based hands-on implementation of Security Mechanisms and Access control


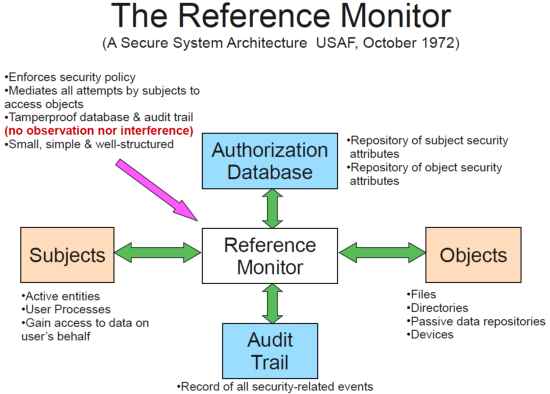






![PDF] Teaching the security mindset with reference monitors | Semantic Scholar PDF] Teaching the security mindset with reference monitors | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/9733b37e5b61ccff306b21907abd3143995c1f8b/2-Figure1-1.png)
