Policy-based access control in application development with Amazon Verified Permissions | AWS DevOps Blog
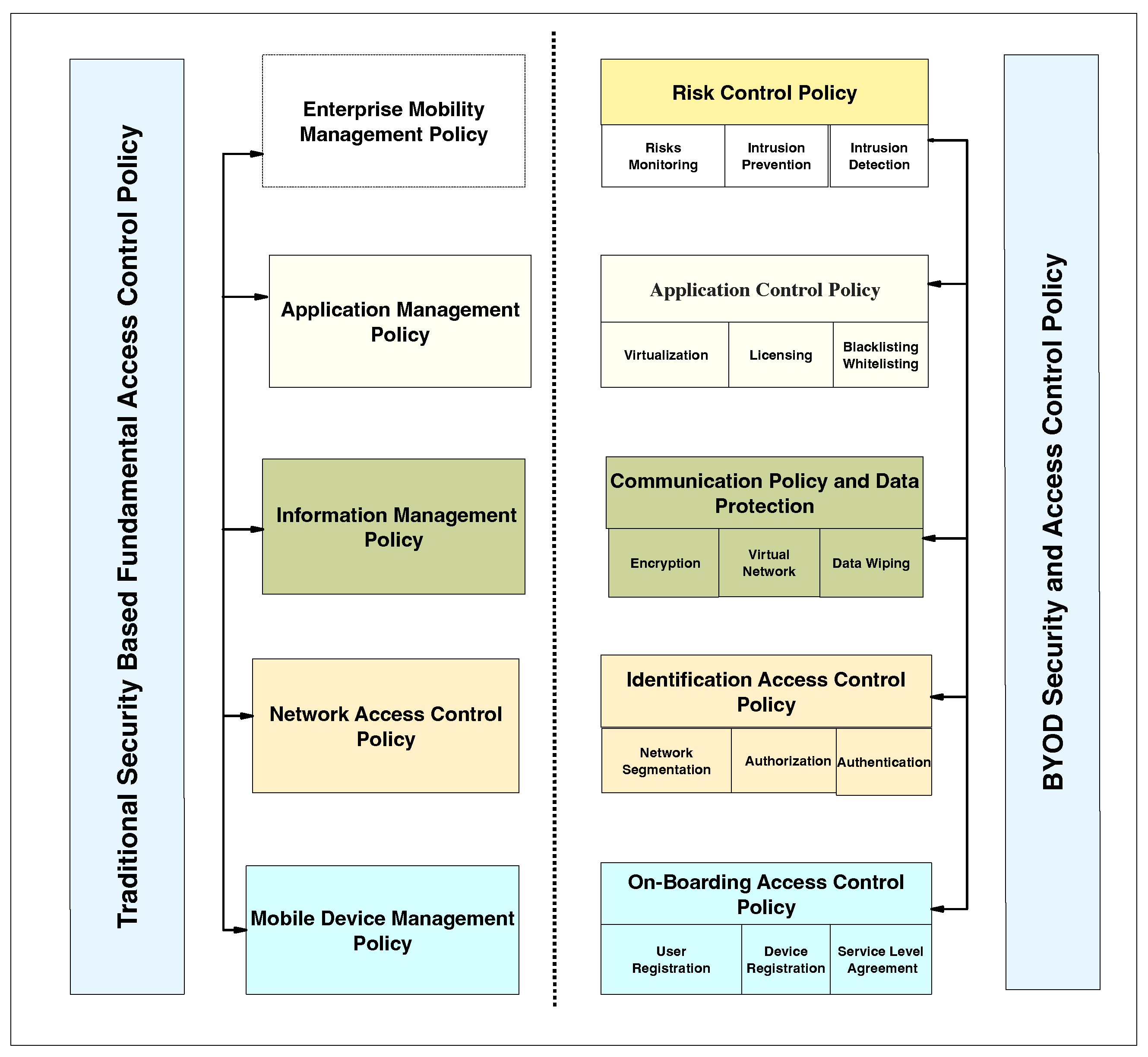
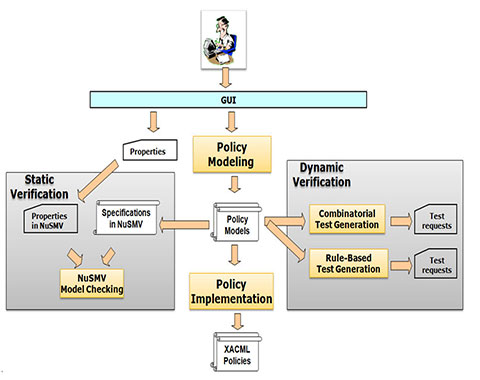
Applied Sciences | Free Full-Text | Systematic Literature Review on Security Access Control Policies and Techniques Based on Privacy Requirements in a BYOD Environment: State of the Art and Future Directions


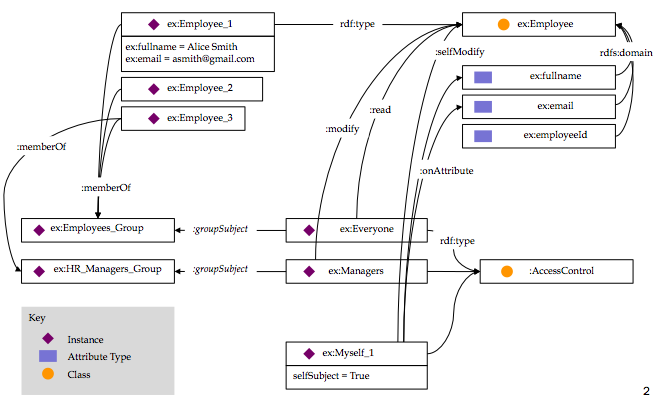

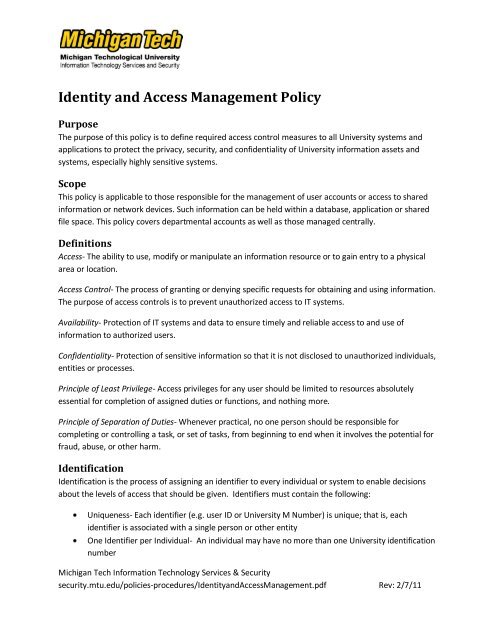




![PDF] Database Access Control Policies | Semantic Scholar PDF] Database Access Control Policies | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/bfd4c8c86b964e3843b853d311181a12267c5633/3-Figure3-1.png)

![Access Control Policy [ISO 27001 templates] Access Control Policy [ISO 27001 templates]](https://advisera.com/wp-content/uploads//sites/5/2021/08/A.9.1_Access_Control_Policy_Premium_Preview_EN.png)